When international conflicts arise — and the world has seen no shortage in recent years — organizations of all sizes need to stay especially alert. In many cases, managed service providers (MSPs) serve as the first line of defense, helping prevent threat activity from reaching their clients’ environments. Periods of geopolitical tension often correlate with an increase in cyber activity, making this a particularly demanding time for cybersecurity professionals.
When international conflicts arise — and the world has seen no shortage in recent years — organizations of all sizes need to stay especially alert. In many cases, managed service providers (MSPs) serve as the first line of defense, helping prevent threat activity from reaching their clients’ environments. Periods of geopolitical tension often correlate with an increase in cyber activity, making this a particularly demanding time for cybersecurity professionals.
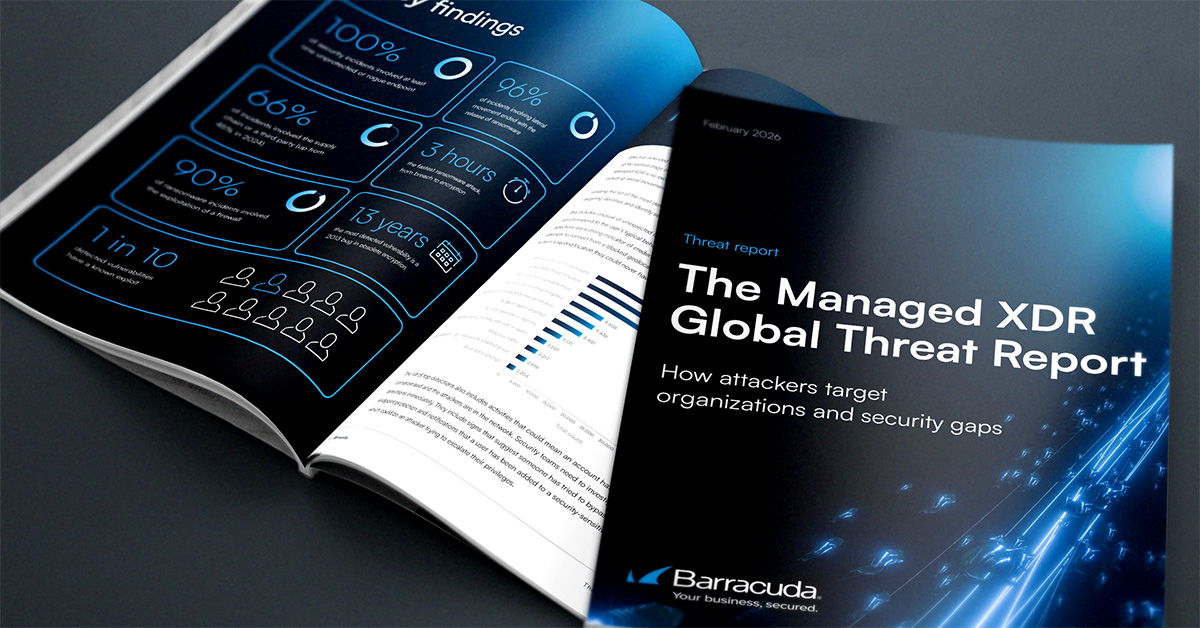
Barracuda Managed XDR’s global SOC has observed significant spikes in malicious network traffic during recent global events. In response, SOC teams often operate at an elevated alert state to protect customers from rapidly evolving risks. At the same time, organizations are advised to reinforce essential security measures to help mitigate exposure.
Why MSPs are on the frontlines
Mary Ann Miller, VP, Evangelist & Fraud Executive Advisor at Prove, shared guidance for MSPs navigating times of heightened international tension.
“The key is to move from awareness to action. Conflicts don’t just increase the volume of attacks; they often change the tactics, with a heavier reliance on identity-based attacks, social engineering, and attempts to exploit trust relationships between vendors and clients,” Miller said.
She noted that MSPs should be particularly vigilant about account takeover attempts, phishing campaigns tied to current events, and unusual login or transaction patterns across client environments.
“Since MSPs often have privileged access to multiple organizations, they are a target — and can serve as a gateway for broader supply chain attacks,” Miller added.
From a proactive standpoint, Miller recommends that MSPs prioritize the following steps:
- Strengthen identity security: Enforce multi-factor authentication across all client environments and eliminate shared or overly permissive credentials.
- Monitor for anomalies: Use continuous monitoring to detect unusual behavior, such as logins from unexpected locations or irregular access times.
- Harden access points: Regularly review and limit administrative privileges, particularly within remote management tools.
- Educate clients: Communicate proactively about emerging threats, especially phishing campaigns that leverage breaking news or global events.
- Test incident response plans: Ensure both MSPs and their clients are prepared to respond quickly and effectively if a breach occurs.
Sector spotlight: Healthcare remains a prime target
Healthcare organizations, in particular, can be vulnerable because of the large volumes of sensitive data they manage, making them attractive targets for attackers.
“MSP focus should be on enabling core security capabilities, such as implementing multi-factor authentication, maintaining an accurate inventory of devices, prioritizing risks to identify critical assets, enabling encryption where possible, and establishing a strong incident response program,” said Shankar Somasundaram. He added that network segmentation is essential to minimize the blast radius of an attack and help ensure continuity across different parts of the environment.
Dan Rearden, SOC Analyst at ProCircular, emphasized the importance of layered security.
“Anomalous user behavior can indicate that an account has been compromised,” Rearden said, pointing to signs such as logins from unexpected locations, use of new devices, or unauthorized VPN activity.
From a defensive perspective, SOC teams rely on ticket history and log data to determine whether user behavior falls outside normal patterns.
“Being on high alert for programmatic logins can also indicate that a user is being phished,” Rearden added. He stressed the value of a defense-in-depth strategy — ensuring that if one security layer fails, others are in place to detect or stop attackers before they can move deeper into the organization.
Rearden also highlighted the importance of enforcing MFA on all accounts — especially administrator accounts — and keeping critical systems fully patched to eliminate known vulnerabilities.
Echoing this message, Andrew Chipman, GRC Manager at ProCircular, noted that MSSPs should consistently encourage clients to patch systems, correct misconfigurations, enforce MFA, and isolate critical systems from direct internet exposure.
Best practices: What security teams should enforce
Barracuda’s experts also recommend the following foundational security measures:
Network Security
- Implement country-level blocking at the firewall for regions where the organization does not conduct business
- Disable public-facing Remote Desktop Protocol (RDP), enforce MFA for all remote access, and monitor logs for failed or unusual login attempts
- Lock out users after three to five failed login attempts and consider virtual desktop infrastructure (VDI) as an alternative to direct RDP access
Firewall Settings
- Review all inbound and outbound firewall rules
- Remove any rules set to “permit any”
Password Policies
- Enforce long passwords (14 characters or more)
- Require complexity, including uppercase and lowercase letters, numbers, and special characters
Other Essential Measures
- Prioritize software updates
- Review applications installed on corporate devices and remove unauthorized or unnecessary tools
- Pay close attention to remote access tools, such as TeamViewer and AnyDesk
For a deeper look at best practices during periods of elevated cyber risk, along with recommended EDR rules designed to protect against active threats, read how Barracuda Managed XDR helps organizations stay secure.
Photo: Summit Art Creations / Shutterstock
This post originally appeared on Smarter MSP.